Topical Track: Security, Privacy, and Trust
Track ID: Topi-03
Description
IoT applications and solutions have essential security and privacy requirements before they can be deployed. The explosion in the number of connected devices poses a significant challenge, as does the diversity of the kind of devices and end uses. This year’s World Forum will again address the component and platform implications for IoT in the context of the full life cycle for security and privacy regimes. It will also address the many security architectures and approaches that have emerged from Government organizations around the world, from the Commercial Market space, and from the Research Community. Across the wide spectrum of use cases there is a need to appropriately balance security and privacy, and it is useful to think of classifications that distinguish the levels required that will need different levels of security and privacy. As an example, these may be thought of as:
- Highly security-centric “life-and-death” applications such as: critical infrastructure; control systems for connected automobiles, railroads, or aircraft; connected healthcare
- Intermediate security uses that include: smart home; routine monitoring of facilities; sports and physical exercise activities that involve tracking such as geolocation
- Casual uses such as: games, entertainment, public virtual reality applications, and aspects of social media and general information services
The topics which the “Security and Privacy Regimes for IoT Track” Presentations, Panels, and Working Group discussions will cover include:
- Achieving secure composability of individually secure and possibly insecure devices and components
- The role of the user in helping to secure their IoT components, e.g., changing default manufacturer passwords
- The role of manufacturers to reveal claims concerning assurances concerning their products and services
- Scalability (for massive number of devices, and as contributors to- and consumers of- big data)
- Adapting Blockchain to include resource-limited IoT devices without compromising security
- Device-associated robustness levels that also deal with the high variations in heterogeneity (such as stationary and mobile infrastructure, smart phones and user terminals, wearables, the wide range of possible sensors and actuator types, and embedded IoT devices)
- Device ownership and component control (accounting for interoperability, regulatory compliance, governance, audit-ability and risk management)
- Remediation for the reigning confusion caused by the proliferation of standards and certification, and the realization that IoT will create new experiences and a vulnerability surface that is not accounted for
- Defense in depth strategies from IP design in the chip through the devices, systems and network to the cloud, including data and device validation and interoperability,
- Testing approaches and procedures that overcome the lack of efficacious and accepted practices including interfacing with and leveraging legacy devices and services; containment against expansion of compromise to other units, systems or networks; effective crypto-agility; defense against advanced threats such as quantum-computing attacks. These also include testing approaches for the differing device lifetimes, and lifecycle support of IoT solutions such as over-the-air firmware and software upgrades
One of the objectives of the Track is to launch future actions and activities that continue beyond the World Forum as part of the IoT Initiative Working Group on “IoT Security and Privacy”.
Sessions
Session 1: Security, privacy and attestation for IoT devices and products. The session will look into how we can assure privacy and security when resournce-limited devices come into play. How do we ensure that software running on the devices have not been tampered with. How do ensure a trusted operation of devices and the sytems connected to them over the whole lifecycle of the IoT devices? The session will also address issues related to confidential computing on IoT devices.
Session 2: Secure integration of IoT devices in Blockchain solutions. Blockchain traditionally uses very heavy computing resources to function properly. However, with handheld and IoT devices becoming commonplace, we need to ensure that IoT sytems can be integrated into blockchain solutions. The session will look at techniques that enable this.
Session 3: Towards effective standards for IoT security. IoT adoption, especially at wide scales, such as smart cities, automotive, home automation or industries requires a robust and flexible set of protocols and standards enabling secure operation of the smart environments. This session will address the existing and on development standards for secure IoT systems, as well as the challenges of future use cases, or the gaps that still need agreement by industry and research.
Session 4: Security assurances by manufacturers for IoT products and solutions. With an increasing number of IoT devices being employed, manufacturers of these devices and solutions associated with them need to assure that these work over the complete lifecycle of the products and solutions. The session will look at how this can be achieved.
Session 5: Privacy of IoT Data: Privacy Management of IoT Data. This session will address the issues with privacy preservation and secure management of data in IoT environments. Compliance with normative environments, anonymization and quantification of privacy and security, selective sharing, data access and IoT data receipts are topics of discussion. Data leaks and their impact will, especially in a extensively connected world, as well as the solutions and approaches to prevent and minimize impact.
Chairs
João Paulo Barraca: Universidade de Aveiro, Portugal
Dr. João Paulo Barraca acts as Associate Professor at UA and Vice-Director of the Masters In Cybersecurity, researcher at IT, member of the Scientific Committee of the DETI Doctoral Program, member of the Executive Board of UNAVE, and scientific coordinator of the Cibersecurity Office at UA. He publishes mostly in the areas of networking, software engineering and cibersecurity. Since 2003, he participated in research projects developing novel concepts, or applying these concepts in innovative products and solutions, involving the design of IoT systems, and secure solutions for distributed software/communication systems. Coordinates the local team of the PRR NEXUS WP7 (Cibersecurity) and the 6GSNS RIGOUROUS project. He coordinated the EU NGI Trust CASSIOPEIA, the Big Data School of the DOPPLER project, is the local coordinator of PTCentroDIH, the METIS cybersecurity project, and of other projects like EU LIFE-PAYT, NetEdge, TWIN, SDRT, and SCALE. addressing challenges related with IoT, Software Defined Networking, 5G and Cybersecurity in Low Latency or Critical infrastructures. He also participated in the SKA System Team, in the LINFRA Team.
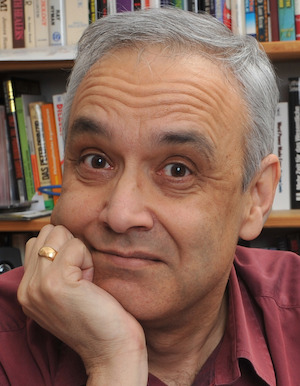
Amardeo Sarma: Trust in Digital Life, Belgium
Amardeo Sarma received his Bachelor of Technology degree from the Indian Institute of Technology, Delhi, in 1977 and his Master’s degree (Diplom-Ingenieur) from the Technical University of Darmstadt in 1980, both in Electrical Engineering. He was at Deutsche Telekom and predecessor from 1981 to 1995, where he participated in several internal and international research projects dealing with signalling, protocols, ATM, middleware and specification techniques. At EURESCOM GmbH in Heidelberg from 1995 – 1999, he supervised projects on software technologies, middleware, ATM and IP. From 1999 – 2001, he was responsible for Technology Management at Deutsche Telekom T-Nova. From April 2001 – June 2023, he was at NEC Laboratories Europe in Heidelberg, where he was involved in topics such as Broadband and mobile networks and Security, Trust, Privacy and Identity Management. He was last employed as General Manager.
Marco Barros Lourenço: ENISA - European Union Cybersecurity Agency, Greece
Marco Barros Lourenco is a technologist and researcher in the field of digital policy. He has a career spanning nearly 30 years, 20 of which were spent in international organisations and multinational corporations such as the World Bank, the EU Council, the United Nations, Microsoft, and the EU Cybersecurity Agency. For nearly two decades, Marco served as an advisor to several governments in Africa, Europe and the Middle East, particularly in the area of digital policy. He helped define national digital and cybersecurity strategies for more than 17 countries. Since 2018, Marco has been responsible for the research and innovation programme for the European Union Cybersecurity Agency (ENISA). He advises the European Commission and Member States on research and digital policy and contributes to the EU's strategic agenda for research and innovation. Marco has an academic background is computer science and business administration with a masters in information security from Portuguese and Belgium universities.
David Goodman: Trust in Digital Life , Belgium
David is director of Identitas Consulting, working in digital transformation, specifically the areas of identity management and cybersecurity, data protection and privacy regulation as well as emerging technologies including artificial intelligence and distributed ledger technologies. He has worked in senior management positions across a wide range of companies in Europe and North America from start-ups (Soft-Switch, Metamerge) to global brands (Lotus Development, IBM, Nokia Siemens Networks and Ericsson) as well as University College London. David is currently a director and senior consultant with Trust in Digital Life association, a principal consulting analyst with TechVision Research, chief marketing officer with iGrant.io, and, until recently, executive director of the Open Identity Exchange (OIX). He was work package leader for dissemination, communication and exploitation, as well as task leader for Open Banking road mapping and use case demonstrators in the CyberSec4Europe H2020 project. David has a BA from the University of Manchester and a D.Phil. from the Oriental Institute, University of Oxford.